Amazon detective analyzes, investigates, and identifies the root cause of security findings or suspicious activities. Amazon Detective for security investigation of Kubernetes Workloads on Amazon EKS makes it easy to respond to security issues. Kubernetes, open-source container orchestration, deploys many individual containers with Amazon Elastic Kubernetes Service (Amazon EKS). These may need more security, and Amazon Detective effectively secures Amazon EKS workloads.
Amazon Detective
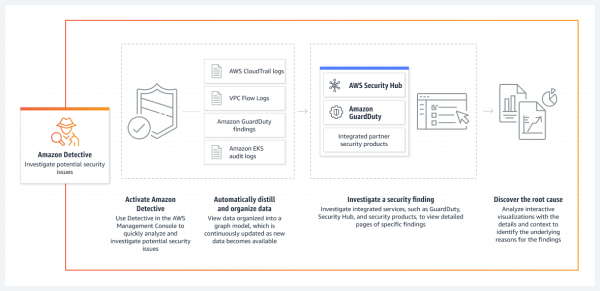
To investigate security issues, Amazon detective collects log data from AWS resources and uses machine learning, statistical analysis, and graph theory to make investigation easier. Detectives help you to find the nature and extent of possible security issues by pre-building data aggregations, summaries, and context. For a selected time window detective provides a visualization layer to view the data variation in volume and type of activity. And the changes are linked to GuardDuty findings.
Detective automatically extracts temporal events like login attempts, API calls, and network traffic from Amazon GuardDuty and Amazon VPC flow logs into graph models. These graphs, give you a summary of resource behavior and interaction observed across the AWS environment. And you will get the details of failed login attempts or suspicious API calls.
Amazon Detective for Security Investigation of Kubernetes Workloads
By enabling Amazon Detective, it will ingest EKS audit logs to examine API activities from users, applications, and the control plane in Amazon EKS for Kubernetes subjects. Below is how it works:
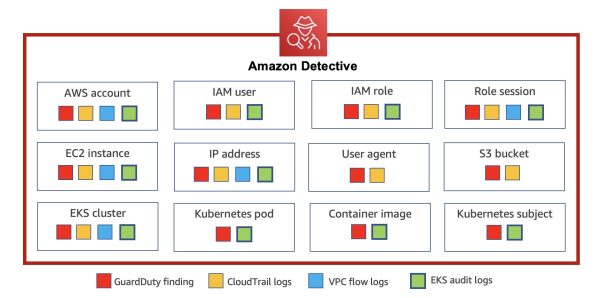
- GuardDuty: Detects malicious activities and unauthorized access
- CloudTrial: Correlates user activities.
- VPC flow logs: Correlates network activities
- EKS audit logs: Allows to add information about resources created with EKS for behavior graphs.
In the case of Amazon EKS clusters, if any malicious activity or threats occurs, Amazon Detective will find and layer them on top of the entity profile with Amazon GuardDuty Kubernetes Protection. Amazon Detective for Kubernetes workloads gives you the details of the Kubernetes API used by the compromised user account, GuardDuty findings on pods hosted in an Amazon EC2, or containers created from malicious container images.
Steps for getting started with security investigation for EKS Audi Logs:
- Enable Amazon Detective with a few clicks on AWA Management Console.
- From the left navigation panel, under Settings, choose General.
- Under Optional Source Package, enable EKS Audit Logs.
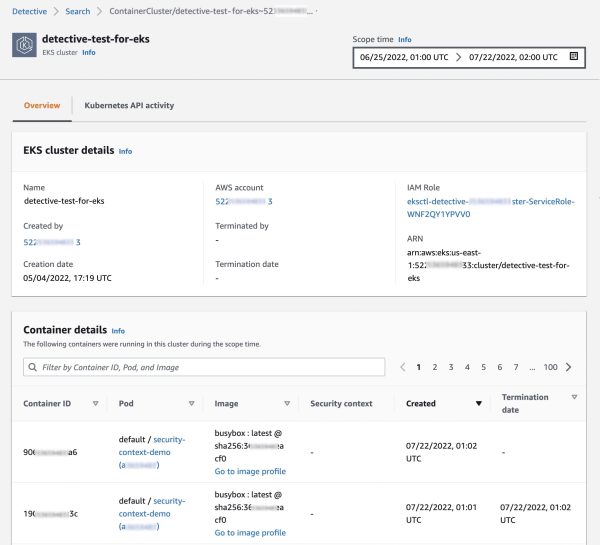
After enabling, Detective will start monitoring the Kubernetes audit logs generated by Amazon EKS for security purposes. Under the Summary page, you can see the recent monitoring results of EKS clusters.

When you click on one of the EKS clusters, you can see the containers running on that cluster, Kubernetes API, and network activities.
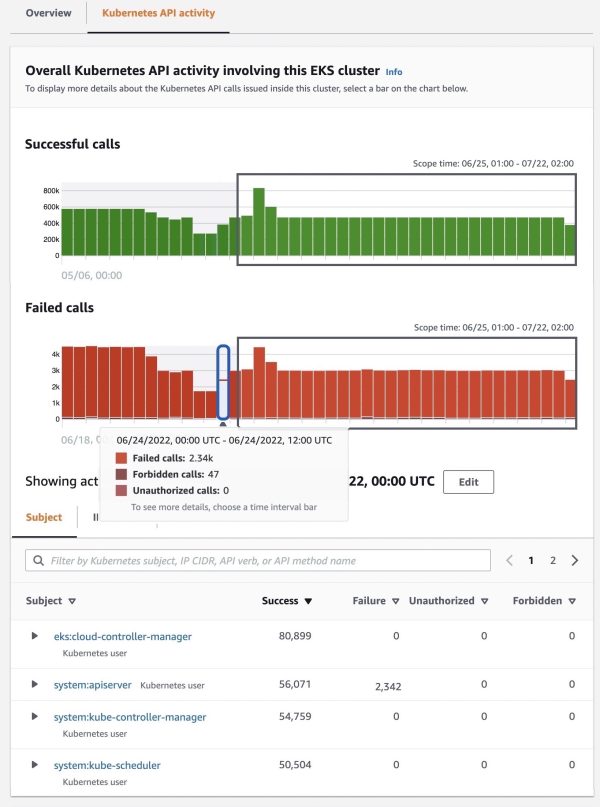
By clicking the Kubernetes API Activity tab, you will get the API activities in the EKS cluster. Select a specific time bar to view successful, failed, forbidden, and unauthorized API calls.
Conclusion
Amazon Detective for security investigation of Kubernetes Workloads on Amazon EKS will give overall security in the AWS consulting Services. And Amazon Detective for EKS is available in all regions where Amazon detective is available. You will get a 30-day free trial of Amazon Detective. During that time, you will get an overview of the monthly cost of the service and coverage for security needs.
Be free to consult Metclouds technology for the security coverage of your Kubernetes workloads with Amazon Detective.


